Archive
The Next Generation of Identity Management
The face of identity is changing. Historically, it was the duty of an identity management solution to manage and control an individual’s access to corporate resources. Such solutions worked well as long as the identity was safe behind the corporate firewall – and the resources were owned by the organization.
But in today’s world of social identities (BYOI), mobile devices (BYOD), dynamic alliances (federation), and everything from tractors to refrigerators being connected to the Internet (IoT), companies are finding that legacy identity management solutions are no longer able to keep up with the demand. Rather than working with thousands to hundreds of thousands of identities, today’s solutions are tasked with managing hundreds of thousands to millions of identities and include not only carbon-based life forms (people) but also those that are silicon-based (devices).
In order to meet this demand, today’s identity solutions must shift from the corporation-centric view of a user’s identity to one that is more user-centric. Corporations typically view the identity relationship as one between the user and the organization’s resources. This is essentially a one-to-many relationship and is relatively easy to manage using legacy identity management solutions.
What is becoming evident, however, is the growing need to manage many-to-many relationships as these same users actually have multiple identities (personas) that must be shared with others that, in turn, have multiple identities, themselves.
The corporation is no longer the authoritative source of a user’s identity, it has been diminished to the role of a persona as users begin to take control of their own identities in other aspects of their lives.
Identity : the state or fact of being the same one as described.
Persona : (in the psychology of C. G. Jung) the mask or façade presented to satisfy the demands of the situation or the environment.
In developing the next generation of identity management solutions, the focus needs to move away from the node (a reference to an entry in a directory server) and more towards the links (or relationships) between the nodes (a reference to social graphs).
In order to achieve this, today’s solutions must take a holistic view of the user’s identity and allow the user to aggregate, manage, and decide with whom to share their identity data.
Benefits to Corporations
While corporations may perceive this as a loss of control, in actuality it is the corporation that stands to benefit the most from a user-centric identity management solution. Large corporations spend hundreds of thousands of dollars each year in an attempt to manage a user’s identity only to find that much of what they have on file is incorrect. There are indeed many characteristics that must be managed by the organization, but many of a user’s attributes go well-beyond a corporation’s reach. In such cases, its ability to maintain accurate data within these attributes is relatively impossible without the user’s involvement.
Take for instance a user’s mobile telephone number; in the past, corporations issued, sponsored, and managed these devices. But today’s employees typically purchase their own mobile phones and change carriers (or even phone numbers) on a periodic basis. As such, corporate white pages are filled with inaccurate data; this trend will only increase as users continue to bring more and more of themselves into the workplace.
Legacy identity solutions attempt to address this issue by introducing “end-user self-service” – a series of Web pages that allow a user to maintain their corporate profile. Users are expected to update their profile whenever a change occurs. The problem with this approach is that users selectively update their profiles and in some cases purposely supply incorrect data (in order to avoid after hours calls). The other problem with this approach is that it still adheres to a corporate-centric/corporate-owned identity mindset. The truth is that users’ identities are not centralized, they are distributed across many different systems both in front of and behind the corporate firewall and while companies may “own” certain data, it is the information that the user brings from other sources that is elusive to the company.
Identity Relationship Management
A user has relationships that extend well beyond those maintained within a company and as such has core identity data strewn across hundreds, if not thousands of databases. The common component in all of these relationships is the user. It is the user who is in charge of that data and it is the user who elects to share their information within the context of those relationships. The company is just one of those relationships, but it is the one for which legacy identity management solutions have been written.
Note: Relationships are not new, but the number of relationships that a user has and types of relationships they have with other users and other things is rapidly growing.
Today’s identity management solutions must evolve to accept (or at a minimum acknowledge) multiple authoritative sources beyond their own. They must evolve to understand the vast number of relationships that a user has both with other users, but also with the things the user owns (or uses) and they must be able to provide (or deny) services based on those relationships and even the context of those relationships. These are lofty goals for today’s identity management solutions as they require vendors to think in a whole new way, implement a whole new set of controls, and come up with new and inventive interfaces to scale to the order of millions. To borrow a phrase from Ian Glazer, we need to kill our current identity management solutions in order to save them, but such an evolution is necessary for identity to stay relevant in today’s relationship-driven world.
I am not alone in recognizing the need for a change. Others have come to similar conclusions and this has given rise to the term, Identity Relationship Management (or IRM). The desire for change is so great in fact that Kantara has sponsored the Identity Relationship Management Working Group of which I am privileged to be a member. This has given rise to a LinkedIn Group on IRM, a Twitter feed (@irmwg), various conferences either focused on or discussing IRM, and multiple blogs of which this is only one.
LinkedIn IRM Working Group Description:
In today’s internet-connected world, employees, partners, and customers all need anytime access to secure data from millions of laptops, phones, tablets, cars, and any devices with internet connections.
Identity relationship management platforms are built for IoT, scale, and contextual intelligence. No matter the device, the volume, or the circumstance, an IRM platform will adapt to understand who you are and what you can access.
Call to Action
Do you share similar thoughts and/or concerns? Are you looking to help craft the future of identity management? If so, then consider being part of the IRM Working Group or simply joining the conversation on LinkedIn or Twitter.
OpenIDM 3.1: A Wake Up Call for Other Identity Vendors
Having implemented Sun, Novell, and Oracle provisioning solutions in the past, the one thing that I found to be lacking in ForgeRock’s OpenIDM solution was an easy to use administrative interface for connecting to and configuring target resources.
Sure, you could configure JSON objects at the file level, but who wants to do that when “point and click” and “drag and drop” is the way to go.
With OpenIDM 3.1 my main objection has been eliminated as the the new resource configuration interfaces have arrived – and boy have they arrived!
 See the OpenIDM Integrator’s Guide for more information.
See the OpenIDM Integrator’s Guide for more information.
The latest release now places OpenIDM directly in line as a viable alternative to the big boys and will make our deployments much quicker and less prone to error. Way to go ForgeRock, thanks for listening (and responding).
Gimme My Damn Data – And Help Me Understand It!
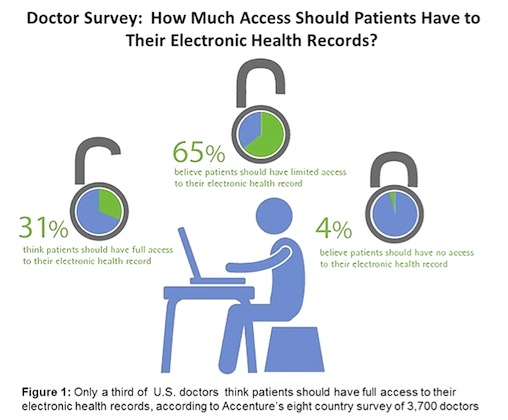
I recently read a Computerworld article that discussed the reluctance of physicians to share patient data with the patients themselves. The article referenced a survey conducted by Accenture and Harris Interactive that found of the 3,700 physicians asked, only 31% felt that patients should have access to their own healthcare records.
“It found that 82% of U.S. physicians want patients to update their electronic health records with information about themselves, but only 31% believe patients should have full access to that record; 65% believe patients should have only limited access. Four percent said patients should have no access at all.”
This can best be represented by the following graphic from the Computerworld article:
This is old school thinking and is akin to asking someone to “show me yours and I will ‘think’ about showing you mine” (but probably won’t). How very one-sided.
When I first joined the Personal Data Ecosystem Consortium (PDEC), I did so because I believed that people should be allowed to take control of their own data. To me, “personal data” was roughly defined as identity and PII data; this was largely due to my identity background. But over the past year this has shifted towards healthcare data and while many of the same thoughts apply, the ROI on managing healthcare data can be much higher as it directly correlates to a person’s primary asset – their health.
Google Health, Microsoft HealthVault, CareZone – there is no shortage of applications designed to assist people in managing their healthcare data. While some efforts have failed, others remain hopeful. But as this survey demonstrates, there is still a long way to go to change the minds of those who are diagnosing and managing this data – the physicians, themselves. If they could only understand that patients are uniquely capable of assisting in the management of their own healthcare; but in order to do so, they need the data (and they need to understand what it means).
Over the past couple of years we have been developing applications that utilize the Lifedash platform. This allows our users to take control of their own data and selectively share it with others. Our latest application is CareSync and it is directly focused on healthcare. We are currently in a beta of the Web application and are piloting our Health Assistant services. Both of these offerings allow people to aggregate and manage their own healthcare in a collaborative environment but allows them to do it safely and securely. The feedback we have received from our participants has been overwhelmingly positive as people are losing faith in the healthcare system. They either want to (or feel forced to) take an active role in managing their own (or family’s) healthcare but to do so, they need the data.
With the reluctance of most physicians to share it is challenging at best. There are, however, techniques that you can use to obtain this information but it requires persistence (the word “nagging” comes to mind). It should not be that way – after all, it is our data.
In the words of healthcare activist e-Patient Dave, just “give me my damn data!” Or as I would add, just “give me my damn data, help me to understand what you just gave me, and tell me how I compare to others in my situation!”
A New Generation of Indentured Servitude
Your digital identity is comprised of information that you volunteer about yourself and information that is observed about you as you simply participate in life. You can (somewhat) control the personal data that you share with others, but have you ever wondered about the type of information that is gathered about you, how long it is retained, and how it is used?
A friend of mine introduced me to a video that provides insight into these questions. It contains an interesting perspective on how your digital identity is comprised, collected and used.
It is interesting to note that almost four years of our lives is owned by someone else – and we willingly give it away. Does that make us indentured servants to those vendors who provide us “free services” in return?
The speaker makes another interesting comment at the end of the video,
The global Internet becomes the personal Internet and information ceases to be information at all.
I am not entirely sure that I agree with that statement; I guess it depends on who it is being made about. Unless we (the ones who generate the data) benefit in the form of better applications, streamlined experiences, or potentially even financial returns, then I don’t see it becoming a “personal Internet” at all.
In our current form of indentured servitude, we continue to give away pieces of our freedom in return for very little.
It is time to turn the model around.
Which Line Do You Want To Be In?
I stumbled across the following image the other day and thought it was too good not to share.
Consider the information that you share with social networking sites on a daily basis. Are you guilty of giving up your privacy in return for things that are transient? I think to some degree we all are. We have become a society that is willing to trade the important things in life for short term gain.
But it is time to ask yourself, which line do you want to be in?
Disjointed Identity
Having my identity located in so many different databases is like wearing multiple watches
You never really know what time it is!
Secret Identities
Methinks that Ziggy secretly works for Facebook.
He is incorrect, however, everyone needs secret identities.
Facebook’s Trolling for Keywords
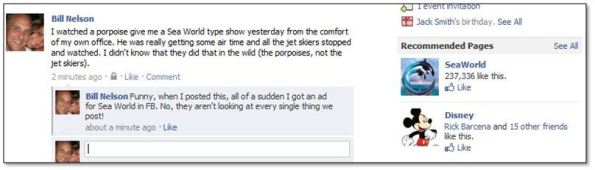
I posted a status to Facebook that included the words “Sea World” and all of a sudden I received a recommended page for Sea World and other Orlando theme parks in their advertisement section. Does anyone really think that Facebook isn’t parsing every post for nuggets they can glean and use for advertising purposes?
From a technical perspective, it is pretty impressive. From a privacy perspective, it is very very scary.