Archive
The Next Generation of Identity Management
The face of identity is changing. Historically, it was the duty of an identity management solution to manage and control an individual’s access to corporate resources. Such solutions worked well as long as the identity was safe behind the corporate firewall – and the resources were owned by the organization.
But in today’s world of social identities (BYOI), mobile devices (BYOD), dynamic alliances (federation), and everything from tractors to refrigerators being connected to the Internet (IoT), companies are finding that legacy identity management solutions are no longer able to keep up with the demand. Rather than working with thousands to hundreds of thousands of identities, today’s solutions are tasked with managing hundreds of thousands to millions of identities and include not only carbon-based life forms (people) but also those that are silicon-based (devices).
In order to meet this demand, today’s identity solutions must shift from the corporation-centric view of a user’s identity to one that is more user-centric. Corporations typically view the identity relationship as one between the user and the organization’s resources. This is essentially a one-to-many relationship and is relatively easy to manage using legacy identity management solutions.
What is becoming evident, however, is the growing need to manage many-to-many relationships as these same users actually have multiple identities (personas) that must be shared with others that, in turn, have multiple identities, themselves.
The corporation is no longer the authoritative source of a user’s identity, it has been diminished to the role of a persona as users begin to take control of their own identities in other aspects of their lives.
Identity : the state or fact of being the same one as described.
Persona : (in the psychology of C. G. Jung) the mask or façade presented to satisfy the demands of the situation or the environment.
In developing the next generation of identity management solutions, the focus needs to move away from the node (a reference to an entry in a directory server) and more towards the links (or relationships) between the nodes (a reference to social graphs).
In order to achieve this, today’s solutions must take a holistic view of the user’s identity and allow the user to aggregate, manage, and decide with whom to share their identity data.
Benefits to Corporations
While corporations may perceive this as a loss of control, in actuality it is the corporation that stands to benefit the most from a user-centric identity management solution. Large corporations spend hundreds of thousands of dollars each year in an attempt to manage a user’s identity only to find that much of what they have on file is incorrect. There are indeed many characteristics that must be managed by the organization, but many of a user’s attributes go well-beyond a corporation’s reach. In such cases, its ability to maintain accurate data within these attributes is relatively impossible without the user’s involvement.
Take for instance a user’s mobile telephone number; in the past, corporations issued, sponsored, and managed these devices. But today’s employees typically purchase their own mobile phones and change carriers (or even phone numbers) on a periodic basis. As such, corporate white pages are filled with inaccurate data; this trend will only increase as users continue to bring more and more of themselves into the workplace.
Legacy identity solutions attempt to address this issue by introducing “end-user self-service” – a series of Web pages that allow a user to maintain their corporate profile. Users are expected to update their profile whenever a change occurs. The problem with this approach is that users selectively update their profiles and in some cases purposely supply incorrect data (in order to avoid after hours calls). The other problem with this approach is that it still adheres to a corporate-centric/corporate-owned identity mindset. The truth is that users’ identities are not centralized, they are distributed across many different systems both in front of and behind the corporate firewall and while companies may “own” certain data, it is the information that the user brings from other sources that is elusive to the company.
Identity Relationship Management
A user has relationships that extend well beyond those maintained within a company and as such has core identity data strewn across hundreds, if not thousands of databases. The common component in all of these relationships is the user. It is the user who is in charge of that data and it is the user who elects to share their information within the context of those relationships. The company is just one of those relationships, but it is the one for which legacy identity management solutions have been written.
Note: Relationships are not new, but the number of relationships that a user has and types of relationships they have with other users and other things is rapidly growing.
Today’s identity management solutions must evolve to accept (or at a minimum acknowledge) multiple authoritative sources beyond their own. They must evolve to understand the vast number of relationships that a user has both with other users, but also with the things the user owns (or uses) and they must be able to provide (or deny) services based on those relationships and even the context of those relationships. These are lofty goals for today’s identity management solutions as they require vendors to think in a whole new way, implement a whole new set of controls, and come up with new and inventive interfaces to scale to the order of millions. To borrow a phrase from Ian Glazer, we need to kill our current identity management solutions in order to save them, but such an evolution is necessary for identity to stay relevant in today’s relationship-driven world.
I am not alone in recognizing the need for a change. Others have come to similar conclusions and this has given rise to the term, Identity Relationship Management (or IRM). The desire for change is so great in fact that Kantara has sponsored the Identity Relationship Management Working Group of which I am privileged to be a member. This has given rise to a LinkedIn Group on IRM, a Twitter feed (@irmwg), various conferences either focused on or discussing IRM, and multiple blogs of which this is only one.
LinkedIn IRM Working Group Description:
In today’s internet-connected world, employees, partners, and customers all need anytime access to secure data from millions of laptops, phones, tablets, cars, and any devices with internet connections.
Identity relationship management platforms are built for IoT, scale, and contextual intelligence. No matter the device, the volume, or the circumstance, an IRM platform will adapt to understand who you are and what you can access.
Call to Action
Do you share similar thoughts and/or concerns? Are you looking to help craft the future of identity management? If so, then consider being part of the IRM Working Group or simply joining the conversation on LinkedIn or Twitter.
Living a Passionate Life
You may (or may not) have noticed that I have been visibly absent from posting over the past few months. The long and the short of it is that quite a few things have happened in my life which have led me to focus on, well…, my life.
The biggest impact was the loss of my mother to lung cancer back in October. For those of you privileged to know her, she was quite the lady and she kept her wit and humor intact to the very end. For the most part, her passing was relatively quick and heaven truly gained an angel that day. She was a profound influence in my life and I will miss her deeply. I kept this event pretty much to myself, but for those of you who were aware and comforted me during this troubling time, thank you. My mom always kept things to herself (including her health issues); maybe I am more like her than I originally thought.
Not long after her passing I had to travel out of the country for business. My journey took me to the island of New Caledonia – a French territory northeast of Australia. That was roughly a 22 hour trip and during that time, I was able to think about my life, where I currently was, and where I wanted to be.
What I realized during that time is that in many areas of my life I was simply going through the motions. I was reminded of the following quote from Steve Jobs,
“The only way to do great work is to love what you do. If you haven’t found it yet, keep looking. Don’t settle. As with all matters of the heart, you’ll know when you find it.”
Our time on earth is too short to live without passion but that is exactly what I was doing – and exactly what I promised myself I would never do. I came to the realization that I was settling in way too many areas of my life and it was time for a change.
pas·sion
noun \ˈpa-shən\
: a strong feeling of enthusiasm or excitement for something or about doing something
They say that you should never make big decisions right after a life changing event, but I have never been one to listen to advice when my heart tells me otherwise. As such, I resigned from my job at Continuum Labs to return to the pursuit of my dreams. Continuum is a great company and I truly believe in their products and services; I just didn’t feel like my contributions were enough to warrant my being there. And those that I was making were not aligned with my passions; it was time for me to reboot my career. I will always be their biggest fan and can only hope that in some small way my tenure has made a positive impact. I will no longer work with my close Continuum friends on a daily basis, but something tells me that we will work together again some day; I look forward to that day. (BTW, if you haven’t had a chance to check out their latest app, CareSync, I HIGHLY recommend it. You will never look at your healthcare the same way again.)
So what am I doing now? My LinkedIn profile says that I am an independent consultant with a company called ForgeRock. What that essentially means is that I am refocusing my career on those areas that make me want to jump out of bed each morning: privacy, identity, trust, and making the Internet a safer place to be. I am continuing to work on the security projects that helped make me Platinum with both Marriott and Delta this year, but I am using my downtime to work on my own security-focused applications and services. While they might not be as sexy as CareSync, I believe there is a definite need for what I am envisioning; but only time will tell. In the meantime, stay tuned.

An unexpected benefit behind all of this is that I am now working at home and am spending more time with my wife and kids. We talk more. I drink morning coffee with my wife, and I am actually there when my kids have a problem. I now see things around the house that need my attention (and what my family has been putting up with as I travel to work each day). Rather than making excuses that I am too tired, I now have the time to fix those things that need fixing. I have the time to make a healthy lunch (or gorge on the box of Oreos if I so desire). I also have time to reboot my exercise life and have the flexibility to take walks with my family as well. Simply put, I have time.
So does this now mean that I will spend this time on blogging, tweeting, and participation in online activities? Maybe. But as with any precious asset, time must be invested properly and spent wisely. With the passing of my mother, I have been reminded that one of the wisest investments you can make is in spending time with others and investing in friendships is never a bad investment.
So who knows where I will devote my time the only thing guaranteed is that it will involve others.
Again, stay tuned.
Gimme My Damn Data – And Help Me Understand It!
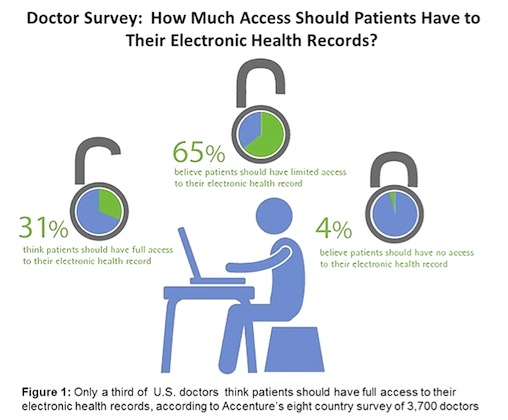
I recently read a Computerworld article that discussed the reluctance of physicians to share patient data with the patients themselves. The article referenced a survey conducted by Accenture and Harris Interactive that found of the 3,700 physicians asked, only 31% felt that patients should have access to their own healthcare records.
“It found that 82% of U.S. physicians want patients to update their electronic health records with information about themselves, but only 31% believe patients should have full access to that record; 65% believe patients should have only limited access. Four percent said patients should have no access at all.”
This can best be represented by the following graphic from the Computerworld article:
This is old school thinking and is akin to asking someone to “show me yours and I will ‘think’ about showing you mine” (but probably won’t). How very one-sided.
When I first joined the Personal Data Ecosystem Consortium (PDEC), I did so because I believed that people should be allowed to take control of their own data. To me, “personal data” was roughly defined as identity and PII data; this was largely due to my identity background. But over the past year this has shifted towards healthcare data and while many of the same thoughts apply, the ROI on managing healthcare data can be much higher as it directly correlates to a person’s primary asset – their health.
Google Health, Microsoft HealthVault, CareZone – there is no shortage of applications designed to assist people in managing their healthcare data. While some efforts have failed, others remain hopeful. But as this survey demonstrates, there is still a long way to go to change the minds of those who are diagnosing and managing this data – the physicians, themselves. If they could only understand that patients are uniquely capable of assisting in the management of their own healthcare; but in order to do so, they need the data (and they need to understand what it means).
Over the past couple of years we have been developing applications that utilize the Lifedash platform. This allows our users to take control of their own data and selectively share it with others. Our latest application is CareSync and it is directly focused on healthcare. We are currently in a beta of the Web application and are piloting our Health Assistant services. Both of these offerings allow people to aggregate and manage their own healthcare in a collaborative environment but allows them to do it safely and securely. The feedback we have received from our participants has been overwhelmingly positive as people are losing faith in the healthcare system. They either want to (or feel forced to) take an active role in managing their own (or family’s) healthcare but to do so, they need the data.
With the reluctance of most physicians to share it is challenging at best. There are, however, techniques that you can use to obtain this information but it requires persistence (the word “nagging” comes to mind). It should not be that way – after all, it is our data.
In the words of healthcare activist e-Patient Dave, just “give me my damn data!” Or as I would add, just “give me my damn data, help me to understand what you just gave me, and tell me how I compare to others in my situation!”
The Dimishing Non-Digital World (or How to get Outed by a Photo Booth)
 I recently attended a high school reunion where a major draw involved the use of a photo booth. You remember photo booths, right? Kiosks where one or more people hide behind a curtain and take pictures of themselves in all sorts of poses. At the end of the session, the kiosk spits out copies of the pictures much to the chagrin of those who aren’t quite as photogenic as they initially thought they were. In our case, reunion attendees were treated to an assortment of funny hats, glasses, and mustaches before entering the booth. They posed with silly expressions, engaged in silly activities, and in some cases even took silly actions to the extreme (I will leave that to your own imagination).
I recently attended a high school reunion where a major draw involved the use of a photo booth. You remember photo booths, right? Kiosks where one or more people hide behind a curtain and take pictures of themselves in all sorts of poses. At the end of the session, the kiosk spits out copies of the pictures much to the chagrin of those who aren’t quite as photogenic as they initially thought they were. In our case, reunion attendees were treated to an assortment of funny hats, glasses, and mustaches before entering the booth. They posed with silly expressions, engaged in silly activities, and in some cases even took silly actions to the extreme (I will leave that to your own imagination).
The point I am trying to make is that once the curtain was closed and the camera light came on people began performing in ways that would be considered unheard of in other settings. Adults who mere minutes before were prim and proper were now raving exhibitionists behind the privacy of a thin veil of cloth. When the curtain was once again opened, they returned to their “normal” behavior and giggled as they left the booth with memories in hand.
So why the sudden change? How did a thin piece of cloth make any difference as to how they acted? The difference was not the curtain, the difference stemmed from their perception of privacy and the context of the situation. People tend to act differently in settings where they feel their actions are private and when the context of the situation is known, they oftentimes let their guard down and act more naturally (or more boldly as the case may be). Just think about Congressman Weiner and his Twitter outing, Alec Baldwin and his fatherly advice to his daughter, or even conversations that you may have had over email, chat, or text when you didn’t think anyone was looking. When people feel more secure in their settings (privacy) and know the rules by which to play (context), they oftentimes act in totally different ways.
The problem with this behavior in a digital society is that you are never truely off the grid and it is all too easy for things to be taken out of context when information is shared inadvertantly. In our current digital society privacy is a facade as few companies take privacy seriously and there are fewer online places where your information is truly secure. Unfortunately, that can also be said of our offline world as more and more of it is becomming digitized as well.
Even within the sacred confines of a photo booth our privacy is not really private at all. Ironically photo booths now take digital photos which are then stored on the kiosk’s computer hard drive. While this expidites the printing process, the possability of those photos being shared with unintended parties is very real. At least that is what I observed shortly after the reunion when pictures from the photo booth began appearing on Facebook. At first I thought that attendees were scanning their own photos and posting them. This thought was immediately dismissed when I saw my own pictures start to appear.
From what I can surmise, the operator of the photo booth provided digital copies of everyone’s photos to one of the reunion committee members who took it upon themselves to post the pictures to Facebook. I am not going to get into the legal, moral, or ethical issues behind this action, but suffice to say, no notice was posted and no permission was granted. Now, I truly believe that those involved had the best intentions of the reunion attendees in mind, but the problem is that they did not have the right to make that decision on their own.
 Intersection cameras, movies on demand (on any device), automobiles that act as WIFI hot spots, Internet connected scales, and yes photo booths – these are only a few examples of how every aspect of our life is becoming affected (or even consumed) by digitalization. All of that content is finding its way into the hands of people who may have good intentions, but who do not understand the ramifications that disclosure of such information may have. As such, they may not take the same care that you or I might take with our own information and may share it with others – all under the guise of good intentions.
Intersection cameras, movies on demand (on any device), automobiles that act as WIFI hot spots, Internet connected scales, and yes photo booths – these are only a few examples of how every aspect of our life is becoming affected (or even consumed) by digitalization. All of that content is finding its way into the hands of people who may have good intentions, but who do not understand the ramifications that disclosure of such information may have. As such, they may not take the same care that you or I might take with our own information and may share it with others – all under the guise of good intentions.
So what happens to our privacy when our information falls into the hands of others? Is it even possible to assume that they have our best intentions in mind when their own companies make money by selling our data to the highest bidder? Can we assume that the context in which we operated is even valid when it may simply be a ruse to get us to let our guards down? Like Rip Van Winkle awaking from his 20 year slumber only to find a world that he no longer recognizes, we too must take care that we resist our own apethetical slumber or we too will wake up to a world we no longer recognize.
A New Generation of Indentured Servitude
Your digital identity is comprised of information that you volunteer about yourself and information that is observed about you as you simply participate in life. You can (somewhat) control the personal data that you share with others, but have you ever wondered about the type of information that is gathered about you, how long it is retained, and how it is used?
A friend of mine introduced me to a video that provides insight into these questions. It contains an interesting perspective on how your digital identity is comprised, collected and used.
It is interesting to note that almost four years of our lives is owned by someone else – and we willingly give it away. Does that make us indentured servants to those vendors who provide us “free services” in return?
The speaker makes another interesting comment at the end of the video,
The global Internet becomes the personal Internet and information ceases to be information at all.
I am not entirely sure that I agree with that statement; I guess it depends on who it is being made about. Unless we (the ones who generate the data) benefit in the form of better applications, streamlined experiences, or potentially even financial returns, then I don’t see it becoming a “personal Internet” at all.
In our current form of indentured servitude, we continue to give away pieces of our freedom in return for very little.
It is time to turn the model around.
Don’t Just Complain, Do Something About It!
A hopelessly lost salesman came upon a farm house where the owner was rocking away on his porch. Late and desperate to get back on the road he stopped to ask for directions.
“Take the dirt road in the direction that the sun sets; keep going until you go past the old post office. Make a left after you drive past the broken down tractor that them Taylor boys left a sittin’ there,” explained the farmer. “Keep a goin’ a bit more until you pass the old sawmill, …” he continued but was interrupted by his old hound dog who let out a rather painful groan.
“Aroooogh,” moaned the dog.
The farmer continued, “…once you get past old McGreevy’s farm, make another left, and …”
“Arooooooogh”… once again, the dog lets out a painful moan.
“Excuse me,” asked the salesman, “but is there something wrong with your dog?”
The farmer looked down at the dog, paused a second, and then replied, “Naw, he’s just lying thar on a nail”. “Wait a minute,” asked the puzzled salesperson, “if he is lying on a nail, why doesn’t he just get up?” Without missing a beat, the farmer said matter of factly, “Don’t hurt enough to get up, just to complain about it…”
Moral: How many times have you criticized someone for how they are doing something? How many problems have you solved with your friends over beers at the local pub? How often do you feel like you have a better idea? Well, stop complaining about it and do something about it!
Remember: “It is better to light a candle than to curse the darkness.”
Trust in Me
Trust in me, I’m the social media vendor providing this FREE service because I want to make you happy. I know that all of this infrastructure and the thousands of employees I have working for me are costing a small fortune, but I do this because I care …. I care about YOU!
Trust in me, I’m the software development company who develops these FREE applications because we are looking out for you. We know that you need something entertaining to do or something informative to occupy your time. We ask you questions about your preferences so that we can customize the software for YOU. That’s the only reason, trust us.
Trust in me, I’m a one man developer operating out of my house creating these FREE applications so that you don’t have to pay for the premium ones. I have no visions of grandeur for myself. I have no dreams of making money for myself, I am doing this for you!
REALLY? No catches at all? Awesome, where do I sign up?
I learned a long time ago that there is no such thing as a free lunch, yet people continue to be duped into believing lies to the contrary. Let me be clear,
Privacy is an illusion in our current social media landscape. Period.
If you think that these FREE services are free then think again; they are anything but. In fact, social media companies and application developers are making money off of the very things that are most precious to you – they are making money by selling information about you and your loved ones. Whether they are selling this information directly or indirectly through advertising, these entities are collecting thousands of pages of information about you – enough to fill volumes of books. Don’t believe me, read Kim Cameron’s article, 24 Year Old Student Lights Match: Europe Versus Facebook.
Your preferences, your habits, your activity – essentially your life – is meticulously tracked by social media sites and used to predict your behavior. With this information in hand, they seek out those who are looking to target those with this behavior or are willing to pay to gain access to these people. It is a well-known fact that social media sites may know more about you than your own family members do, but social media is not the only culprit. “Real world” businesses have been tracking your behavior for years and are just as savvy as social media sites (see How Target Figured Out A Teen Girl Was Pregnant Before Her Father Did). The amount and types of data associated with social media sites is much greater than that obtained in brick and mortar stores as it is more plentiful, easier to gather, easier to store, and easier to analyze.
In George Orwell’s book, 1984, we were worried about a Big Brother that we feel never came. In reality, however, he came and brought his whole family with him and they are all watching us. Get used to it, or take the steps necessary to protect your information assets the same way you protect the money in your bank or your legal documents.
Last month, I wrote a blog entry entitled Which Line Do You Want To Be In? in which I stated that people are
willing to trade important things in life for short term gain
Unfortunately when convenience and privacy are at odds with each other, people tend to throw privacy out the window in trade for convenience. Are these people oblivious or do they simply feel that they have no choice. Have they made a conscious decision or are they simply uneducated to the risks associated with privacy breaches? I tend to believe that most people are too trusting and do not know (or simply do not understand) what information is collected about them and what happens when their information is inadvertently shared. You can classify these people based on age and/or knowledge of technology as follows:
- Typical Kids – who do not yet understand privacy implications
- Typical Adults – who may understand privacy, but don’t understand technology and how it can affect their privacy
- Tech-Savvy Adults – who understand privacy AND take an active role in protecting themselves on social media sites
For those of you who fall in the third category, I know that I am preaching to the choir here, but unfortunately the vast majority of people do not attend the church where this message is being preached. There are still many people who have never heard the message or if they have, they simply choose to ignore it. Is it because they disagree that information is being tracked? Or is it maybe that privacy policies on most social media web sites are simply too difficult to read and/or understand and it is simply easier just to “click through” to get to the site that we want.
I once heard that marketing agencies build their message so that a person with a 7th Grade education can understand it. That is an unfortunate statement to the intelligence of the average American. Unfortunately, it is also a statement that many companies rely on when crafting their legal documents.
Suffice to say, if the price is FREE, it may be costing you dearly.
It Happened One Night
I used to be on the road quite a bit teaching classes or consulting with customers. While the cities were many and the customers diverse, the one thing that was always the same was my music collection – it went with me wherever I went (and continues to do so today).
I was in California on one such event doing work for Sun Microsystems. While listening to my Eagles playlist one particular morning, I was inspired to write this little diddy. The words just flowed and I finished before the first student arrived. I hope you enjoy reading it as much as I did writing it.
(Words are mine, songs are from one of the greatest bands of all time – The Eagles.)
So, I left the customer site last night and headed back to my hotel. You know, my HOTEL CALIFORNIA. It was late in the evening (as usual) and as luck would have it, I came face to face with an OUTLAW MAN in Sun’s parking lot (damn security). He asked me to hand over all my money, but as luck would have it, I had already been robbed that day – by my wife – the WITCHY WOMAN.
I told him to TAKE IT EASY as I reached for the few coins that I had in my pocket. He asked me IS IT TRUE that this is all I had? I responded, yes, there are TOO MANY HANDS in my pocket and he would just have to GET OVER IT. Thank goodness that he felt sorry for me (being the NEW KID IN TOWN and all) and felt that any further effort would simply be WASTED TIME.
When I finally reached the hotel, I found two PRETTY MAIDS ALL IN A ROW (my wife and daughter) and one lone DESPERADO – (my son) who was in trouble because of his LYIN’ EYES (I am glad that he is only three, otherwise he would have landed in a TEENAGE JAIL). My wife relayed her story to me and I to her. Her story paled in comparison to mine and she questioned, IS IT TRUE? (You see, she had caught me in the past CHUGing ALL NIGHT with the GIRL FROM YESTERDAY and she doubted my story)? To which I responded, I CAN’T TELL YOU WHY – IN THE CITY – there’s a HEARTACHE TONIGHT, but that’s what you get when you live LIFE IN THE FASTLANE.
As I look back over the whole event, and look at all the things on this earth that are OUT OF CONTROL, I had to laugh. Because in THE LONG RUN, LIFE’S BEEN GOOD, and even when you TAKE IT TO THE LIMIT, it is still just a GOOD DAY IN HELL so you might as well get that PEACEFUL EASY FEELING and LEARN TO BE STILL.
(Links added for your listening pleasure; not all songs available on MP3.)